- Introduction
- Configuration
- Keys
-
Email Clients
- Basic Email Client Configuration
- Outlook XP/2002
- Modifying Outlook XP/2002
- Outlook 98/2000/Express
- Modifying Outlook 98/2000/Express
- The BAT
- Modifying The BAT
- Pegasus
- Modifying Pegasus
- Eudora
- Modifying Eudora
- Calypso
- Modifying Calypso
- IncrediMail
- Modifying IncrediMail
- Netscape Mail
- Modifying Netscape Mail
- Technical
-
FAQ
- What email clients work with SecExMail ?
- Does SecExMail work with IMAP?
- How secure are SecexMail keys ?
- Is SecExMail legal in my country ?
- Does SecExMail support signatures ?
- Does SecExMail work with PGP ?
- Is the source code available for SecExMail ?
- Why can I not mix clear text and cipher recipients ?
- About
| Top Next |
Email Encryption for Windows
What is SecExMail

SecExMail - Secure Email Made Easy
Maintaining your privacy on the net is not easy in today's world. Until now, secure email could only be achieved by encryption solutions that were not user friendly. SecExMail changes all that, bringing you secure encrypted email that is so easy to use, you will forget it is there!
Advantages at a Glance
Auto key management - no more sending public keys and having to import your friend's keys
Easy to use - no need to change how you work in order to start sending secure email
Automatic - SecExMail encrypts messages if you have the recipients key, otherwise the message is sent in plain text
HTML Filtering - Everybody gets spam and some of it contains malicious code or "call home" features so the spammer knows you opened the mail and will send more spam. SecExMail can filter out the HTML tags so you see plain, harmless text
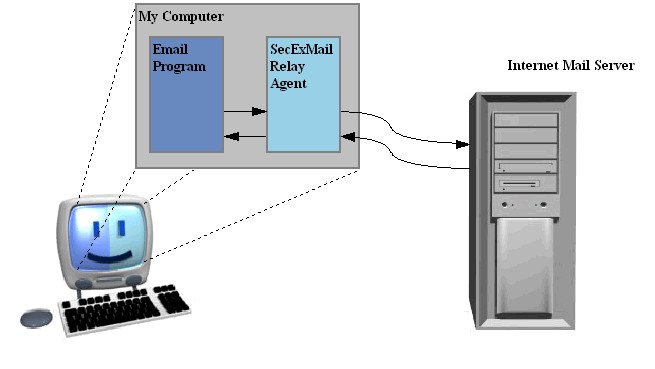
SecExMail implements open standard encryption algorithms to create a seamless security framework to protect the privacy of your email on the public internet. SecExMail operates as a relay agent between your email client to your mail server encrypting and decrypting email streams in real-time and therefore requires no additional plugin software for your favorite email client program.
How SecExMail works :
General Features :
Easy to configure
SecExMail requires no plugins or other email client specific software. Simply configure SecExMail to communicate
with your email server and set your favorite email client to talk to SecExMail. That's it.
Seamless integration
Probably the greatest obstacle to wide-spread use of secure email is that most encryption systems don't integrate seamlessly with popular email clients. In some cases the use of plugins means that encrypted messages held in mail folders are not searchable via the standard email client interface. In other cases, encrypted messages held in mail folders become irretrievable once the encryption plugin is unloaded. In most cases security is an after-thought and the normal work flow is disrupted to accommodate security. Because SecExMail operates unobtrusively in the background, encrypting and decrypting email streams to and from your email client in real-time, you continue to work with your email client as usual.
Fail Safety
Many plugin based encryption systems require the user to treat secure mail differently from ordinary mail. Some require the user to remember that mail to a specific recipient should always be encrypted and take special action to invoke the encryption. If the user forgets, the message is sent in plain text and confidential information may be compromised. Equally, if a plugin is accidentally unloaded or crashes, sensitive information may be compromised because messages designated secure are inadvertently spilled onto the internet in clear text. SecExMail is engineered from the ground up to provide fail safety. Because SecExMail acts as a relay agent or mail proxy and requires the email client to be configured to communicate with its mail server via this proxy, a failure in SecExMail simply means that no mail is sent until the error condition is alleviated. Once the public key for a particular recipient is entered into SecExMail, all mail to that recipient will be sent encrypted by default and without further user intervention.
Proactive Security
SecExMail does not stop at simply encrypting your email messages. It also provides for message stealth at the protocol level. The information contained in the header of most emails provides a wealth of information to the cryptanalyst. For example, the header contains a subject line which tells the cryptanalyst which messages are worth examining. Furthermore the header contains information about the type of message being sent, the so called "MIME type". The MIME type indicates to the cryptanalyst if the message contains only text or perhaps a photograph and if so in what format the photograph is stored ( JPG, GIF, etc ). The latter can be exploited in a known plain text attack. For this reason, SecExMail not only encrypts the message subject but also obscures MIME type information. This means a hacker can neither deduce whether the message is worth examining nor what file attachments, if any, are being sent.
Easy Key Handling
Exchanging keys with friends and business associates is child's play. SecExMail has a built in "one touch" SMTP client and automatic key update feature to facilitate easy distribution of SecExMail keys.
Protect Account Information
Most conventional email communication involves the exchange of clear text passwords. This means that anyone with the right wire tapping equipment, or in fact any skilled system administrator working for your telecommunications company, can collect your password information and subsequently read all your email without your knowledge. SecExMail can protect your user and password information by encapsulating all email traffic in a Secure Socket Layer ( SSL ) or Transport Layer Security (TLS) tunnel. See Mail Server configuration for details. (Offshore and Corporate edition only )
Trojan Horse Protection
SecExMail protects against attempts to trick you into revealing your password information to third parties. See IP/DNS spoofing for technical details. (Offshore and Corporate edition only )
Key Transparency
SecExMail is engineered with a focus on transparency to give you the assurance that no backdoor keys or key recovery is embedded in encrypted messages. See Key Transparency.
Technical Features :
Public Key Encryption
SecExMail uses standard RSA based public key encryption. Supported key sizes are 2048, 4096 and 8192 bits ( up to 10240 bits for offshore edition and corporate edition ). Two messages are never encrypted with the same session key. Instead the public key associated with the recipient of a message is used to encrypt a random session key which is used to encrypt the message. Generation of strong session keys is based on a sophisticated entropy collection system.
Message Encryption
Individual messages are double encrypted via 64 bit ISAAC and 256 bit Twofish encryption . See SecExMail Cipher.
Coexistence with other encryption standards
SecExMail encrypts the mail stream and therefore does not interfere with existing methods of encryption. As such, it is possible to encrypt with PGP or GPG first, and then send the resulting cipher text through SecExMail for further encryption. On the remote end, the recipients SecExMail restores the PGP cipher text which can then be decrypted by the user's email client or associated PGP decryption module.